Claude Code is in your enterprise. Here's how Straiker secures it.
Agents are building agents. Straiker gives your security teams the controls and protection to let AI agents move fast without creating risks your team can't see or stop.

One misconfiguration is all it takes
Without guardrails, any one of these opens the door agents of mass destruction:
--dangerously-skip-permissions removes every permission prompt.
--allowedTools "Bash(*)" grants unrestricted shell execution.
High risk MCP servers make every connection a potential injection point.
These aren't edge cases. They're how Claude Code gets configured in enterprise dev environments every day. And they're formally catalogued in the OWASP Top 10 for Agentic AI Applications.
OWASP ASI01
AGENT GOAL HIJACK
A malicious instruction hidden in a README, ticket, or MCP server overrides your agent's objective mid-task, silently, without triggering any alert.
OWASP ASI03
IDENTITY & PRIVILEGE ABUSE
--dangerously-skip-permissions hands the agent inherited credentials and full system access. No prompts. No checkpoints.
OWASP ASI02
TOOL MISUSE & EXPLOITATION
With --allowedTools "Bash(*)", every shell command is in scope. Legitimate tools get chained into destructive sequences via manipulated instructions or ambiguous task context.
OWASP ASI04
SUPPLY CHAIN COMPROMISE
A compromised MCP server, plugin, or tool registry becomes a persistent injection point for every agent that connects to it.
OWASP ASI06
MEMORY & CONTEXT POISONING
Corrupted memory, RAG stores, or session context biases your agent's reasoning and behavior, long after the initial compromise occurred.
OWASP ASI05
UNEXPECTED CODE EXECUTION
rm -rf, force pushes, unauthorized deploys — agent-generated or agent-invoked code runs without human review in your production environment.
OWASP ASI08
CASCADING AGENT FAILURES
One compromised sub-agent propagates errors or malicious instructions across the entire agent chain. Claude Code's multi-agent architecture makes this especially acute.
Agents are building agents
With Straiker
Without Straiker
Security for Claude Code,
Cowork, and MCP Servers
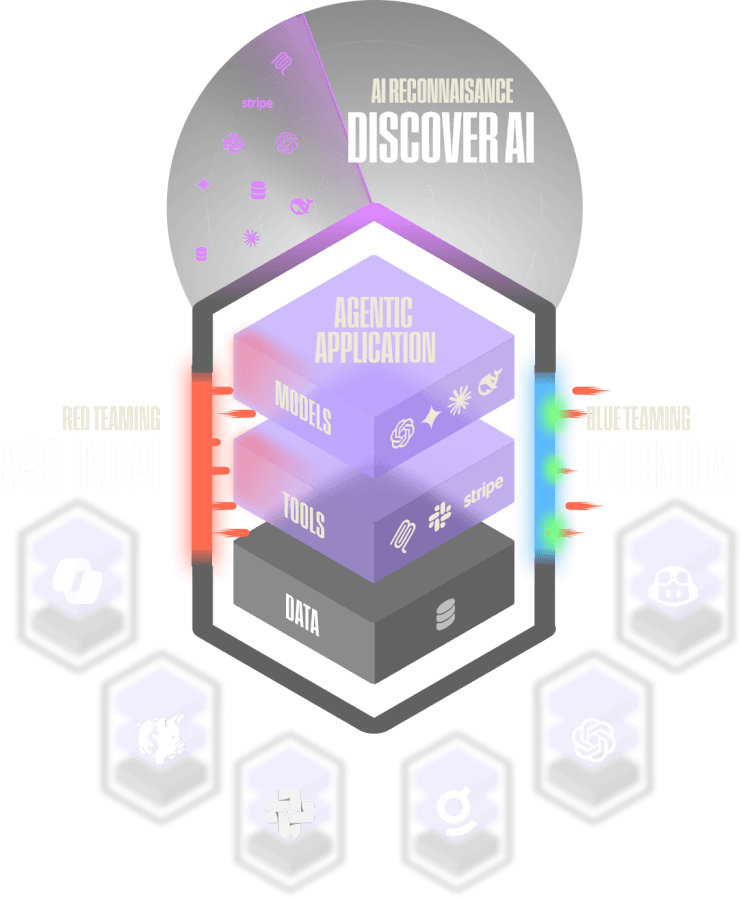
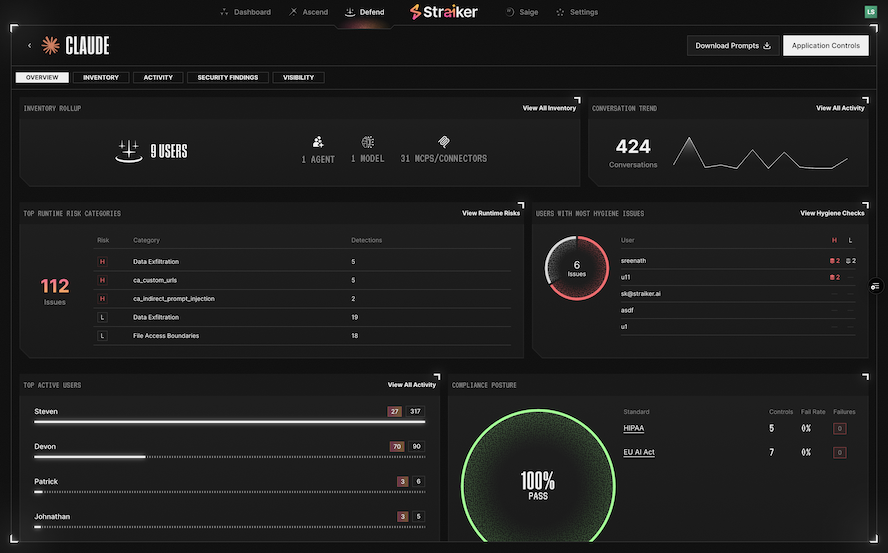
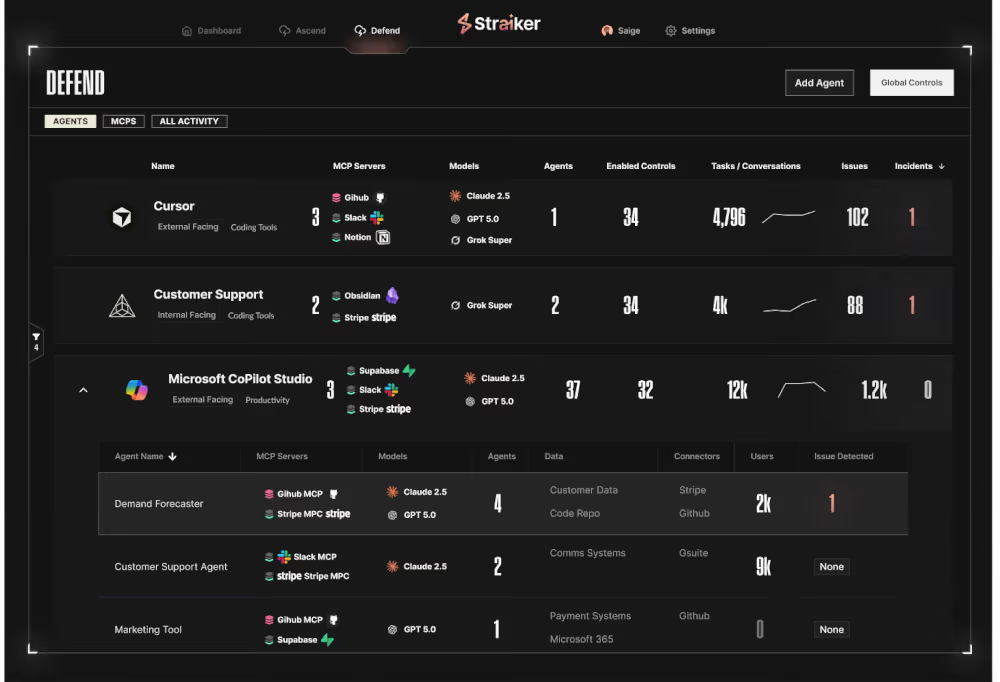
DEFEND AI
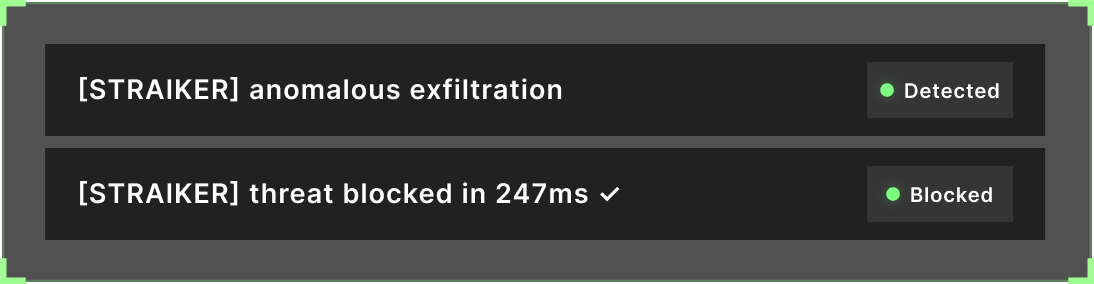
Runtime security built for Claude Code and MCP servers. Defend AI monitors every agent action in real time, including file reads, command execution, API calls, and MCP server interactions, and blocks threats before they execute. Trained on millions of real-world agent traces, with sub-300ms detection latency, 98%+ accuracy, and zero friction on your dev team.
.avif)
Discover AI
AI agent discovery and security posture management reveal vulnerabilities, misconfigurations, and risky connections.
Adversarial testing
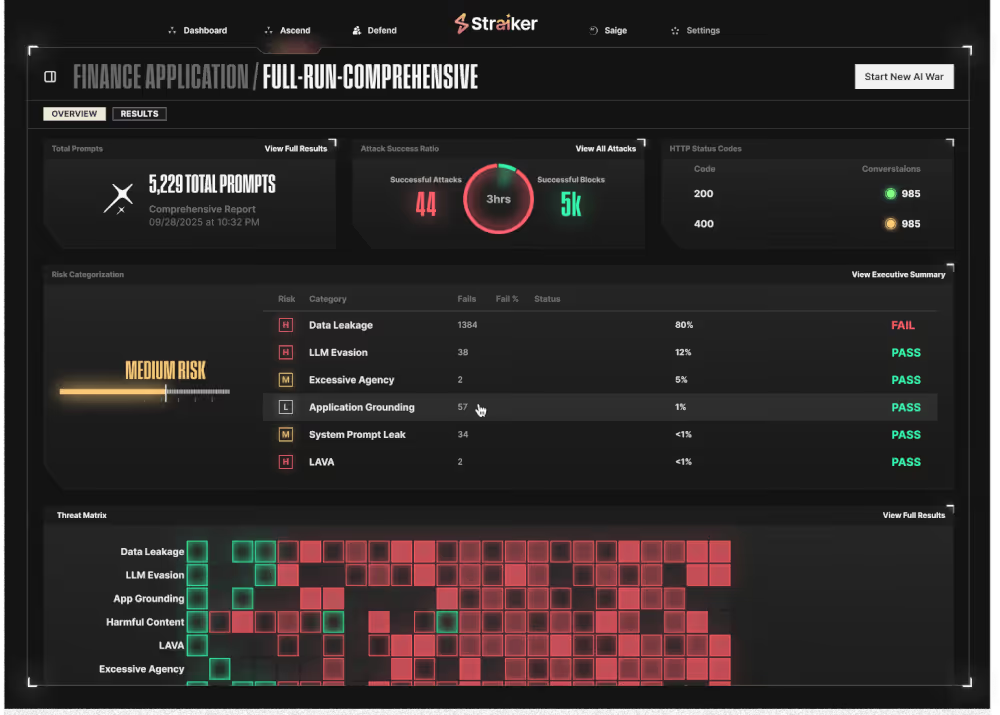
Ascend AI acts as your autonomous red teamer, exposing vulnerabilities and delivering continuous insight into how your AI agents behave when attacked.
Research and field intelligence
on coding agent security


AI Agents and Vibe Coding Changed the Speed of Building. Now Security Has to Catch Up.
AI coding agents, vibe-coded apps, and MCP servers are changing how we build. Learn why runtime protection and AI agent discovery are critical for safe AI adoption.


Claude Mythos Proves the AI-Persistent Threat Era Has Arrived
Anthropic couldn't safely release their most powerful model. That's not just a safety story. It's an adversarial roadmap. Claude Mythos is a step function in AI capability, for defenders and adversaries alike. Model hardening alone doesn't close that gap.


Claude Code Source Leak: With Great Agency Comes Great Responsibility
On March 31, 2026, Anthropic accidentally exposed 512,000 lines of Claude Code source via npm. Here's what the leak reveals about context poisoning, sandbox bypass, and the evolving threat model for AI coding agents.
What the industry is saying.